ExactTrak
IN THE SPOTLIGHT
Published: Jun 04, 2024
In response to the ever-evolving digital threat landscape, The Digital Operational Resilience Act (DORA) aims to strengthen IT security within the financial sector. The EU regulation goes into effect on 17th January 2025. Read on to see why DORA compliance is so important, and how you can achieve it…

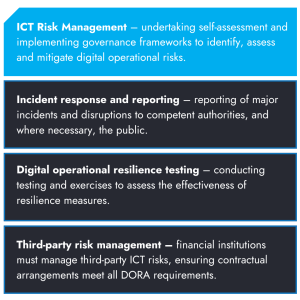
DORA applies to both financial institutions and third-party providers that offer critical services to the sector. Covering a wide range of digital operational risks, from cyber threats and IT failures to data breaches and third-party dependencies, it’s hoped the act will become the standard format of protection for financial organisations across Europe.
The cybercriminal industry (and it is an industry) clearly divides into those who are:
It’s a major step forward to see the financial services sector uniting to counter rising cyber threats. And a much needed step at that. The more information shared, the better the response, resulting in financial entities with better ICT protocols, practices and procedures.
The new age of working from home has caused some major challenges, and placed huge pressure on CISO officers; attack fatigue, difficulty retaining control of widely distributed data access points, education of all employees and maintaining their diligence, and the recruitment and retention of security IT professionals, just to name a few.
We’re sure that news of DORA has probably got your alarm bells ringing – it has the potential to be a massive drain on your already tight IT resources. But that’s where we can offer some help…
Here at ExactTrak, we specialise in data protection and security solutions at the end-point. Whilst a solid network security, threat detection, mail protection, education and other measures are needed to build a strong cyber security system, ExactTrak’s solutions can help you to immediately address DORA’s 1st Pillar (ICT Risk Management) by providing;
SmartSafe provides protection across multiple devices autonomously, requiring limited operational input, and user education.
With the deadline less than a year away, it’s time to take action; failure to meet this legal compliance requirement will result in regulatory sanctions, reputational damage, and increased operational risks and legal liabilities.

It’s the only embedded solution that provides security at device level and full integration with your existing security tools, to provide a multi-layered approach to cyber security.
Learn more
You can set control policies and manage devices remotely, to prevent data exploitation from AI bots and insecure networks, on the move.
Learn more
Allows you to locate, monitor and control devices, anytime, anywhere – even when the power is off – for round the clock protection.
Learn more